
Tracking Volt Typhoon, State-Sponsored Threat Activity Against Critical Infrastructure
February 19, 2024
Read More
Overwhelmed by Vulnerabilities? Contextualizing OT Threats with Risk Based Vulnerability Management
February 8, 2024
Read More
CMMC for OT: Working with the DoD as an Industrial Organization
November 28, 2023
Read More.png)
Qatar Calls for ISA 62443 Compliance in Electric & Water Utilities
October 27, 2023
Read More
Does it Take a Pair of SOCs to Manage Both IT and OT Security?
October 24, 2023
Read More
Taking the Tedious out of Compliance & Governance with Automated, Centralized OT Asset Data
August 2, 2023
Read More
What Is NERC CIP: The Ultimate Guide
July 14, 2023
Read More
OT Cybersecurity: The Ultimate Guide
April 25, 2022
Read More
CVE-2021-44228 - Industrial Defender update on log4j
December 14, 2021
Read More
Video: Monitoring Building Management Systems with Industrial Defender and Splunk
April 21, 2021
Read More
Feature Focus: Building Management System (BMS) Security and Risk Monitoring
November 23, 2020
Read More
4 Benefits of Implementing a Cybersecurity Solution for Building Management Systems
September 23, 2020
Read More
Feature Focus: Asset Risk Scoring Methodology & Netflow Application
October 15, 2020
Read More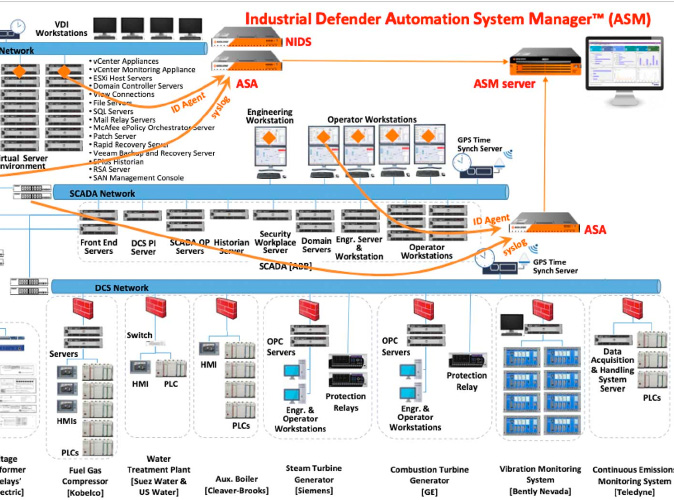
Video: Deploying Industrial Defender Agents on ICS and SCADA Systems (Part 2)
May 28, 2020
Read More
Video: How To Monitor High-Value OT Assets in Microsoft Power BI
July 13, 2020
Read More
Video: Deploying Industrial Defender Agents on ICS and SCADA Systems (Part 1)
May 15, 2020
Read More
Podcast: CTO Phil Dunbar Talks About the Return of Industrial Defender on the Waterfall ICS Security Podcast
March 23, 2020
Read More
Operationalizing Cyber Programs for Industrial Control Systems - 5 Real World Use Cases
April 7, 2020
Read More
Video: Integrating 3rd Party Monitoring Tools with Industrial Defender
April 21, 2020
Read More
Video: Scanless Vulnerability Monitoring for ICS Environments
March 13, 2020
Read More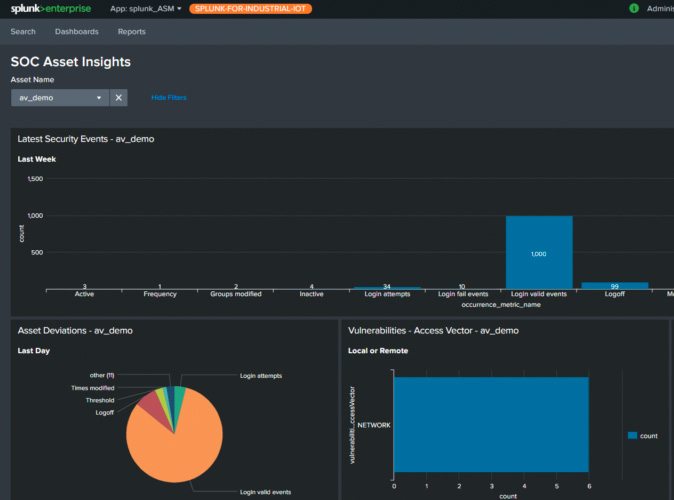
Video: OT SOC Enablement with Splunk
June 25, 2020
Read More
Critical Infrastructure targeted by Russian Government Cyber Activity
March 23, 2018
Read More
Top 5 ICS Security Best Practices
April 3, 2023
Read More






